INDUSTRIAL SAFETY &
ACCESS CONTROL
Automate safety enforcement for every machine and restricted zone.
Ensure hazardous equipment and restricted areas only become accessible when personnel present verifiable proof of training, authorization, and real-time compliance.
Sphereon provides the automated enforcement layer for high-risk environments. Our platform sits between your workforce data and your physical access points—from machinery controllers to secure zone entries. We verify the integrity of digital evidence, check real-time trust status, and apply your safety policies to return an immediate access decision directly into your existing PLCs and building management systems.
The gap in traditional safety controls
Inconsistent manual checks
Visual inspections of paper certificates or plastic badges are prone to human error.
Relying on manual oversight in high-pressure environments leads to bypassed safety protocols and increased operational risk for both personnel and equipment.
Invisible credential expiration
Expired or revoked certifications are nearly impossible to catch at the point of access.
Static badges cannot signal a change in compliance status in real-time, allowing unauthorized workers to enter restricted zones or operate hazardous machinery.
Unverifiable evidence trails
Incident investigations often lack the cryptographically defensible proof required for audits.
Without an automated, immutable log of the exact credentials presented during an access event, proving regulatory and insurance compliance becomes a significant liability.
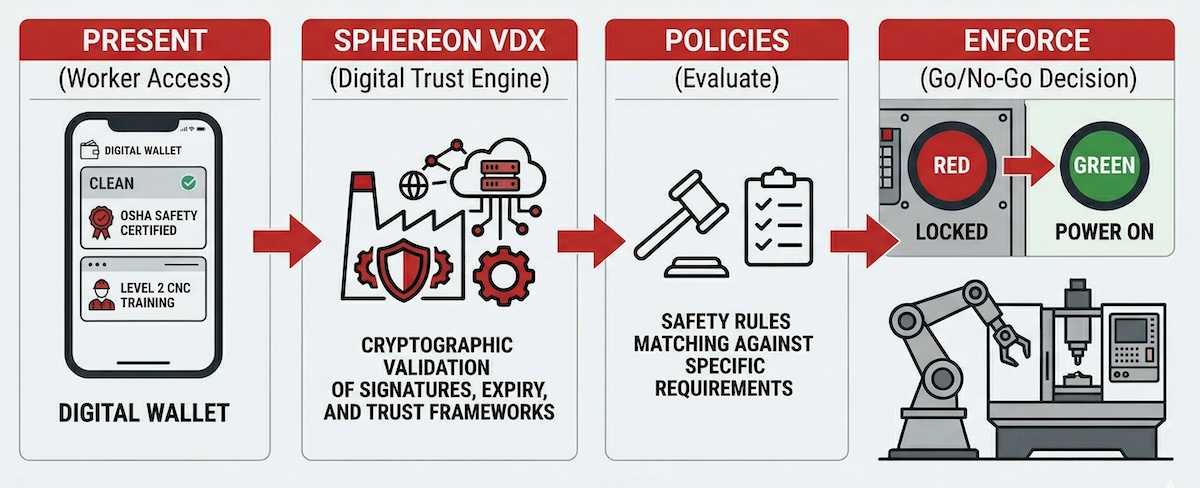
From presentation to power-on: how it works.
1. Present
Worker presents digital credentials via smartcard or phone with NFC/BLE.
This initiates a cryptographic user-bound exchange at the physical machine controller or zone entry point.
2. Verify
Proofs are checked against trust and safety policies in real-time.
Sphereon VDX instantly validates cryptographic signatures, expiry status, and specific access or certification requirements.
3. Enforce
A secure “Go/No-go” decision is returned to the access control system.
The machine unlocks or the gate opens only if all policy requirements are valid and authentic.
4. Log
Audit-ready evidence is generated for every access event or attempt.
Every access decision is recorded as an immutable proof of compliance for safety and insurance.
Operational verification capabilities
The system enforces safety by instantly validating the specific attributes required for secure access.
Verified identity
Cryptographic certainty that the person at the machine or zone entry is the authorized holder of the credential.
Machine-specific training
Validation of technical competencies required to operate specific hazardous equipment (e.g., CNC, high-voltage, or heavy machinery).
Safety certifications
Real-time proof of valid VCA, OSHA, or internal safety protocols required for high-risk industrial environments.
Site induction
Confirmation that site-specific safety briefings and legal waivers have been completed and signed by the worker.
Contractor affiliation
Proof that external personnel belong to an authorized vendor and that their employer’s insurance and compliance are current.
Real-time validity status
Instant verification that a credential has not been revoked or expired since it was issued, preventing use of stale data.
Operational outcomes
Reduce unsafe access
Technically prevent the operation of hazardous equipment by unauthorized personnel.
Eliminate the risk of “accidental” or uncertified use of machinery and unauthorized entry into high-risk industrial zones.
Automate authorization
Remove the administrative bottleneck of manual paperwork and badge updates.
Real-time credential verification ensures that permissions are updated instantly across the entire facility without human intervention.
Audit-ready evidence
Satisfy NIS2, insurance, and regulatory requirements automatically.
Every access event generates an immutable, cryptographically signed log, providing a defensible evidence trail for post-incident investigations.
Operational outcomes
Reduce unsafe access
Eliminate unauthorized operation: Ensure that hazardous equipment and restricted zones are physically locked until a valid, user-bound credential is presented.
Automate authorization
Replace manual oversight: Remove the lag of physical badge management and manual certificate checks with a real-time, automated policy engine.
Audit-ready evidence
Defensible compliance: Generate immutable logs of every access decision that satisfy the strict reporting requirements of NIS2 and safety insurers.
Ready to automate your industrial safety?
Speak with our team to see how Sphereon VDX integrates
with your specific machinery and access systems.