Audit-Ready Evidence
for NIS2 Compliance
Automate the proof of your duty of care.
Move beyond manual reporting and best-effort narratives. Sphereon generates the cryptographically certain audit trails required to protect your organization—and its leadership—from the management liability risks defined in NIS2.
Replace manual record-keeping with immutable evidence that satisfies national regulators.
By automating the “burden of proof,” you shift compliance from a periodic headache to a continuous, defensible state of assurance.
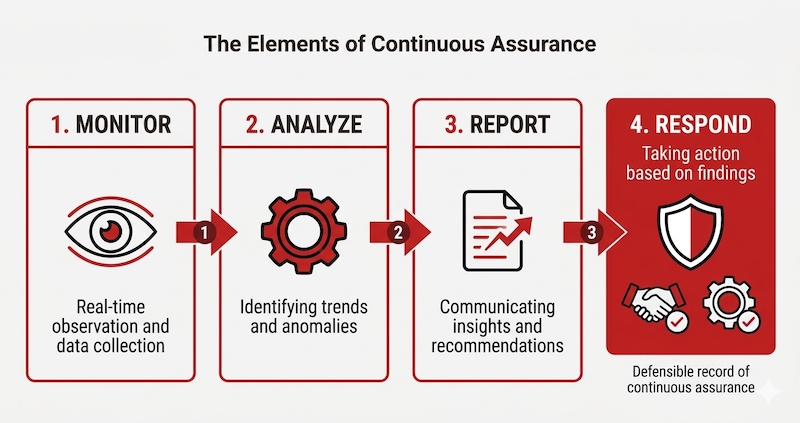
The elements of continuous assurance
Context-rich authorizations
Prove exactly who was authorized, under which specific mandate or role, at the precise moment of access. Capture the full legal and organizational context of every decision, not just the technical result.
Policy-driven logic
Demonstrate the specific safety or security rule that was applied. This moves compliance from a narrative “best effort” to an auditable, repeatable logic that eliminates human error and manual overrides.
Independent auditability
Provide regulators and insurers with cryptographic evidence they can validate independently. This removes the need for them to “blindly trust” your internal databases or manual spreadsheets.
Tamper-proof chronology
Replace manual incident reconstruction with a real-time, immutable timeline. This is critical for meeting the 24-hour and 72-hour reporting windows required under NIS2 Articles 21 and 23.
How verifiable evidence maps to NIS2 technical requirements.
The following table demonstrates how the architecture converts high-level regulatory pressure points into specific, auditable technical outcomes.
| NIS2 pressure point | Sphereon control contribution | Evidence retained |
|---|---|---|
| Management liability (Art. 20) |
Automated enforcement of “Duty of Care” (Zorgplicht) policies across all digital interactions. | Proof of “best-practice” technical controls and governance-linked authorizations for liability mitigation. |
| Supply chainsecurity (Art. 21) |
Replaces manual questionnaires with cryptographic proofs for suppliers, mandates, and certifications. | Requested proof, trust context, verification result, and policy outcome. |
| Incident reporting (Art. 23) |
Enables 24/72-hour reporting by preserving a verifiable chronology of authorizations and access events. | Timeline of proof requests, accepted/rejected evidence, and affected business decisions. |
| Risk management (Art. 21) |
Shifts from ad-hoc exceptions to repeatable, policy-driven decisions that are easier to test and explain. | Consistent decision records and verifiable audit trails for internal or external review. |
| Cryptography (Art. 21) |
Integrates with QTSP and HSM providers to ensure key custody is handled in regulated, high-assurance environments. | Signing context, key provider paths, and associated business event metadata. |
Download the Architecture brief PDF →
For internal review and technical due diligence by Enterprise Architects and Compliance teams.
Read the Architecture brief Online →
Explore the technical bottom line of our trust control plane directly in your browser.
Bridging the gap between intent and evidence.
Under NIS2, having a security policy is only half the battle. The other half is proving it was actually enforced.
Traditional compliance relies on “intent”—policies, manual logs, and retrospective screenshots. But regulators now demand “evidence.” This means proving that a specific access decision or data exchange was justified by a valid credential and a real-time policy check.
Sphereon shifts your organization from reactive reporting to continuous assurance. We provide the mathematically undeniable proof that your Duty of Care was met at the precise moment it mattered, protecting both your operations and your leadership from regulatory and personal liability.
The intersection of NIS2 and eIDAS 2.0
While NIS2 defines the security obligations for essential and important entities, eIDAS 2.0 provides the technical standard for meeting them.
By using the European Digital Identity Wallet (EUDI) framework, Sphereon ensures your compliance isn’t just “audit-ready” for today: it is natively aligned with the upcoming legal requirements for cross-border digital identity and verifiable credentials.
We help you build a trust infrastructure that satisfies both security regulators and identity standard regulations at the same time!
Partner insight:
“Many organizations make the mistake of treating NIS2 as an isolated IT project.
A strategic partner understands that identity is the new perimeter.
By solving for eIDAS 2.0 and NIS2 at the same time, you reduce architectural complexity and long-term compliance and implementation costs.”
Stop chasing evidence.
Start leading compliance.
Stop the manual reconstruction of security events. Let’s discuss how to
integrate an automated trust layer that turns NIS2 from a regulatory burden
into a measurable, strategic advantage for your organization.