Designed for Developers
Developer ecosystem for digital trust.
Build, deploy, and scale verifiable credential infrastructure with modular tools designed for every stage of the development lifecycle.
Sphereon provides a comprehensive suite of tools for engineering teams working on decentralized identity. From open-source libraries for custom wallet development to production-grade enforcement runtimes and managed cloud services, our ecosystem is built on open standards like OID4VC and SD-JWT.
Choose the level of control your project requires and move from concept to production with cryptographically verifiable certainty.
Choose your development path
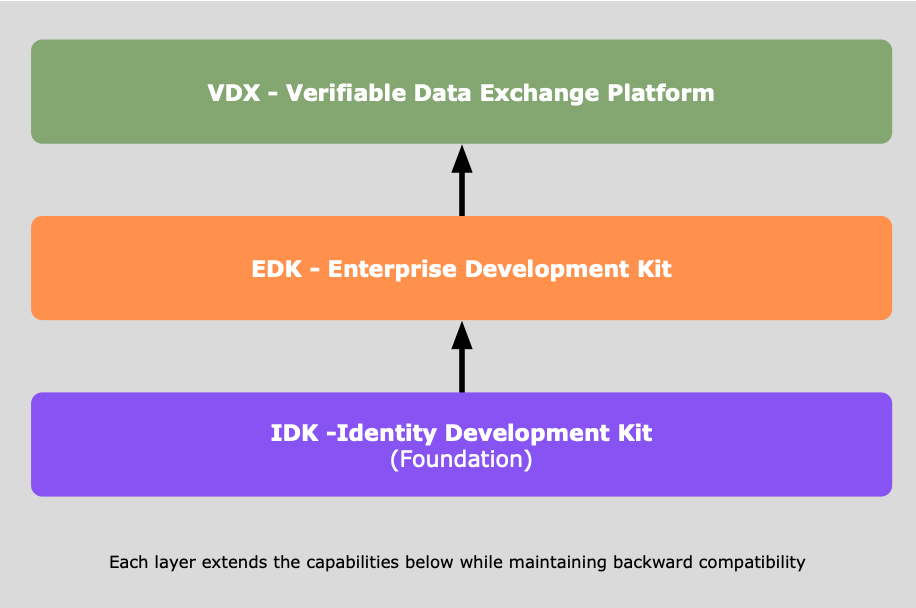
Sphereon IDK
Open-source SDK libraries for credential protocols and cryptography. Build custom wallets and agents with fine-grained control over the identity foundation and protocol implementation from a single codebase.
Sphereon EDK
Containerized runtimes and enforcement engines for production environments. Deploy high-performance infrastructure with HSM-backed secure key custody, database adapters, and robust compliance auditing out of the box.
Sphereon VDX platform
An API-first orchestration platform for verifiable data exchange. Built for enterprise flexibility with multiple deployment models, including fully managed cloud, self-hosted, and high-security on-premise installations for total sovereignty.
The path from code to compliance: how it works.
1. Discover
Explore our developer docs and discover our open source standards approach.
Understand how OID4VC, SD-JWT, and decentralized identifiers form the basis of your trust architecture.
2. Build
Integrate IDK libraries into your application to handle credential lifecycles.
Develop custom wallet experiences or specialized agents using high-performance Kotlin or TypeScript.
3. Scale
Transition to production with EDK runtimes or the VDX platform.
Move beyond local development to secure, containerized environments with HSM-backed key custody and persistent storage.
4. Enforce
Implement real-time policy control and generate auditable evidence.
Connect your identity infrastructure to physical and digital access points to automate safety and compliance.
Need technical guidance?
Our engineering team is ready to help you architect your solution,
from protocol selection to production deployment.